Hacker Mode
Explore the world of hacking & cybersecurity
About this course
Uncover the realm of cybercrime! Students learn essential skills to explore the dynamic landscape of cybersecurity and sort the real from the fake.
Rooted in real-world examples and hands-on exercises, Hacker Mode equips students with an understanding of hacker behaviours. Students are challenged to find solutions to hacks using logic, fundamental programming skills (teen course), as well as creativity and resourcefulness.
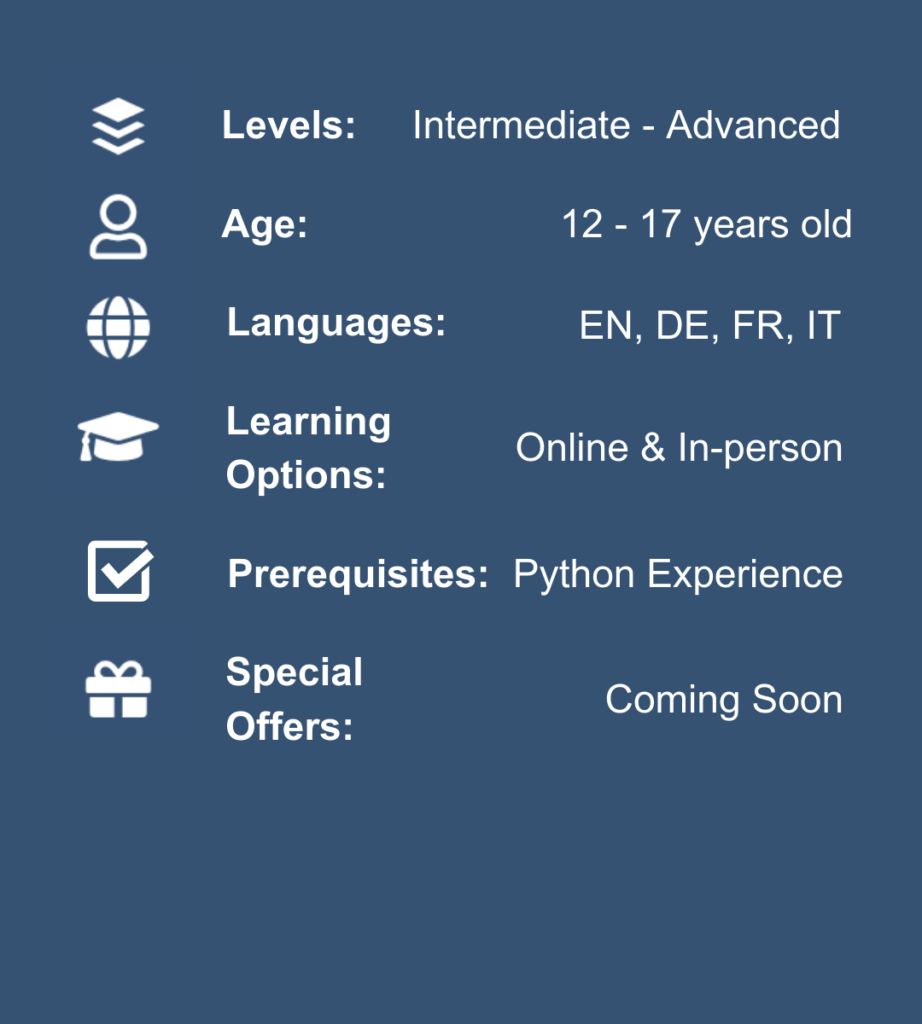
Levels:
Intermediate – Advanced
Age:
12+
Languages:
EN, DE, FR, IT
Learning Options:
Online & In Person
Prerequisites:
Python Experience
Special Offers:
Coming Soon
Discover Our Learning Options
-
ONLINE 1:1
TUTORING -
ONLINE GROUP
CLASSES -

IN-PERSON
CAMPS
Explore a topic of your choice at your own pace with private 1:1 online tutoring lessons.
Learn new skills in semi-private online classes with live
instructor guidance & peer interaction.
Join our Swiss camps to learn in a fun environment with adaptive
teaching styles and 1:5 tutor-student ratio.
- LAUSANNE
- GENEVA
- ZURICH
- ZUG & LUZERN
July 8-12, 2024 (5 days)
Collège Champittet
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
July 15-19, 2024 (5 days)
Collège Champittet
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
Aug. 12-15, 2024 (4 days)
Collège Champittet
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
July 8-12, 2024 (5 Days)
Institut Florimont
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
July 16-19, 2024 (4 Days)
Institut Florimont
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
Aug. 19-23, 2024 (5 Days)
Institut Florimont
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
April 22-26, 2024
(5 Days)
Freies Gymnasium Zürich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00 – 15:30 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
April 29 - May 2, 2024
(4 Days)
Bleicherweg 27, Zurich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
9:30 – 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
July 1-5, 2024 (5 Days)
Bleicherweg 27, Zurich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
9:30 – 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
July 15.19, 2024 (5 Days)
Freies Gymnasium Zürich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00 – 15:30 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
Aug 13-16, 2024 (4 Days)
Bleicherweg 27, Zurich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
9:30 – 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
April 23-26, 2024 (4 Days)
Haus Zum Lernen
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00– 15:30 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
Aug. 12-14, 2024 (3 Days)
Haus Zum Lernen
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00– 15:30 daily
Camp fees:
Juniors 525CHF
Teens 655CHF
Discover Our Learning Options
Explore a topic of your choice at your own pace with private 1:1 online tutoring lessons.
Learn new skills in semi-private online classes with live instructor guidance & peer interaction.
Join our Swiss camps to learn in a fun environment with adaptive
teaching styles and 1:5 tutor-student ratio.
July 8-12, 2024 (5 days)
Collège Champittet
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
July 15-19, 2024 (5 days)
Collège Champittet
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
Aug. 12-15, 2024 (4 days)
Collège Champittet
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
July 8-12, 2024 (5 Days)
Institut Florimont
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
July 16-19, 2024 (4 Days)
Institut Florimont
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
Aug. 19-23, 2024 (5 Days)
Institut Florimont
Semi-private camp with 3-6 students per class, lead by top EPFL/ETHZ instructors.
Camp hours:
09:30– 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
April 22-26, 2024
(5 Days)
Freies Gymnasium Zürich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00 – 15:30 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
April 29 - May 2, 2024
(4 Days)
Bleicherweg 27, Zurich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
9:30 – 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
July 1-5, 2024 (5 Days)
Bleicherweg 27, Zurich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
9:30 – 15:00 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
July 15.19, 2024 (5 Days)
Freies Gymnasium Zürich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00 – 15:30 daily
Camp fees:
Juniors 890CHF
Teens 1080CHF
Aug 13-16, 2024 (4 Days)
Bleicherweg 27, Zurich
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
9:30 – 15:00 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
April 23-26, 2024 (4 Days)
Haus Zum Lernen
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00– 15:30 daily
Camp fees:
Juniors 790CHF
Teens 910CHF
Aug. 12-14, 2024 (3 Days)
Haus Zum Lernen
Semi-private camp with 3-6 students per class, lead by top ETHZ instructors.
Camp hours:
10:00– 15:30 daily
Camp fees:
Juniors 525CHF
Teens 655CHF
Experienced Instructors from Europe's Best Universities
Experience has shown that the best way to get youth into digital technology is through fun, accessible learning. All our programs are led by inspiring young instructors from Europe’s Top 10 Technical Universities – carefully selected for their ability to explain complex notions and engage with students.
We know teaching style can make a world of difference, our focus is on creating, not lecturing. All our modules are developed in-house by our experienced educators and focus on hands-on, project-based learning, using industry-standard software & accredited educational tools.
The TechSpark Advantage
Our reviews speak for themselves!
Do you have any questions? We are here to help!
Easy answers to common questions:
- As cybercrime costs increase exponentially, understanding prominent cyber threats and cultivating responsible online behaviour is increasingly important.
- Our Cybersecurity curriculum is crafted to be both informative and enjoyable, providing practical insights into the realm of hackers.
- “Hacker Mode” equips students with essential skills to detect fakes and navigate the digital landscape securely.
- The Hacker Mode curriculum is based on a problem-solving approach. The focus is on student’s ability to solve cybersecurity problems, creating an atmosphere where students are eager to apply the learning, because solving cybersecurity puzzles is fun!
- The course’s focus is on simplifying the complex world of cybersecurity, with an emphasis on an instructor’s role as a coach. This results in a powerful learning loop, met with overwhelmingly positive feedback from our students.
- Through engaging hands-on activities and real-world scenarios, our “Hacker Mode” cybersecurity course not only imparts critical cybersecurity skills, but also instils a sense of empowerment, making the learning experience both informative and enjoyable.
- We encourage students to think like a cyber security professional: Cybersecurity training is brought to life through real-world hacking challenges and puzzles. Our gamified exercises will show students how programs work and train them to think critically.
- Students experience the thrill of cybersecurity competitions: PicoCTF “Capture The Flag” (CTF) is a hacker’s competition designed by Carnegie Mellon University and targeted to middle and high school students. Students are presented with a vulnerable system, which can be hacked to retrieve a piece of information (the flag).
- Students learn to use their computer’s terminal line, turning it into something functional instead of a mysterious black box (OpenClassRooms).
- Finally, students’ critical thinking about today’s cybersecurity world is fostered: Over multiple sessions, students will view/listen to a documentary, movie or podcast tackling relevant real-life cybersecurity events, and discuss them as a team.
- To ensure all students get the most out of their TechSpark experience, we ask ALL students to take a short (5 mins) Computational Evaluation the beginning of their first lessons. This allows our instructors to tailor the course material to the student’s needs.
- If you select a course or level which does not correspond to your child’s knowledge, don’t worry – we can recommend another course and/or will adapt accordingly, depending on the group size for our online or in person class.
- Noteworthy: Our Cybersecurity course is designed for students with previous Python experience. Do check our Python curriculum for preparatory courses
- TechSpark Academy prides itself in its Swiss quality, with dedicated instructors from top Swiss and European universities, creating a comfortable and adaptive learning environment.
- Our online private tutoring caters to individual styles, promoting deep understanding and confidence.
- Online classes and camps in Switzerland’s most beautiful locations are limited to 5-6 students per group, and provide personalized attention for a supportive atmosphere, ensuring mastery of concepts.
Get advice from our experts!
Contact our specialists for advice on finding the right learning option, course or camp for your child.
Our partners:




Other Courses Students Love: